[ad_1]
After I first began utilizing Linux, again in ’97, working with the built-in firewall was not one thing simply anybody might do. The truth is, it was fairly difficult. Beginning round 1998, if you wish to handle the safety of a system, you needed to be taught iptables (which is a set of instructions for manipulating the Netfilter packet filtering system).
For instance, if you wish to enable all incoming safe shell (SSH) visitors, you might need to challenge instructions like this:
sudo iptables -A INPUT -p tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT sudo iptables -A OUTPUT -p tcp --sport 22 -m conntrack --ctstate ESTABLISHED -j ACCEPT
That is all superb and good when you have time to not solely grasp the Linux working system, but additionally know the finer factors of managing an advanced safety system. To be truthful, I did spend the time and was ultimately capable of handle the safety of my methods with iptables.
Nonetheless, the busier I received, the tougher it grew to become to proceed the extent of mastery wanted to maintain up with iptables. Over time, issues began getting extra accessible and a few Linux distribution builders started to appreciate a neater system was vital. A type of extra accessible Linux firewalls got here into being with the Ubuntu distribution (round model 12.04). That firewall is aptly named Uncomplicated Firewall.
Uncomplicated Firewall (UFW) is a frontend for iptables, which focuses on simplicity. In comparison with iptables, UFW is a leisurely stroll via the park that anybody can deal with.
Let’s take a stroll down UFW lane and see simply how easy it makes managing your Linux system firewall.
There are two issues it is best to find out about UFW:
- It is a command-line device.
- There are GUI instruments accessible to make it even simpler.
The UFW command-line fundamentals
The UFW command is definitely fairly easy. Let’s keep on with our SSH concept from above. To illustrate you wish to enable different methods to entry your machine by the use of SSH (which listens on port 22).
First, you may wish to see if UFW is even enabled. Guess what…it isn’t by default. Check that out by opening a terminal window and issuing the command:
sudo ufw standing
You may most likely see the next:
Standing: inactive
How do you activate it? Difficulty the command:
sudo ufw allow
The output of the command needs to be:
Firewall is lively and enabled on system startup
Congratulations, your firewall is now lively.
As to the essential utilization of UFW, it appears one thing like this:
sudo ufw ARGUMENT SERVICE
The place ARGUMENT is both enable, deny, reject, restrict, standing, present, reset, reload, allow, disable and SERVICE is the service you wish to work with (resembling SSH or HTTP).
Subsequent, we have to enable SSH visitors into the system. Consider it or not, that is so simple as:
sudo ufw enable ssh
You can additionally run the command utilizing the port quantity, like this:
sudo ufw enable 22
Or, if you happen to run SSH on port 2022, that command can be:
sudo ufw enable 2022
In the event you’re engaged on a server and you could enable HTTP visitors via, that command can be:
sudo ufw enable http
Let’s get a bit extra superior
one of many good issues about UFW is that even utilizing extra superior options would not require superior data. To illustrate, for instance, you wish to enable SSH visitors in, however solely from a particular IP tackle in your community.
In the event you’ve already allowed incoming SSH visitors, you may first have to delete that rule with:
sudo ufw delete enable ssh
Now, if you happen to attempt to SSH into the machine, the firewall will block the try. So, let’s enable SSH connections from IP tackle 192.168.1.152. For that, we might challenge the command:
sudo ufw enable from 192.168.1.152 to any port ssh
After working the above command, it is best to have the ability to log into the machine, through SSH, solely from the distant system at IP tackle 192.168.1.152.
What in regards to the GUI?
If the command line is not your jam, there’s at all times a useful GUI device to make it even simpler. One such device is GUFW, which lets you level and click on your option to UFW firewall guidelines. If UFW is not put in in your Linux distribution by default, you may discover it in your app retailer. As soon as put in, open the app and click on on the Guidelines tab (Determine 1).
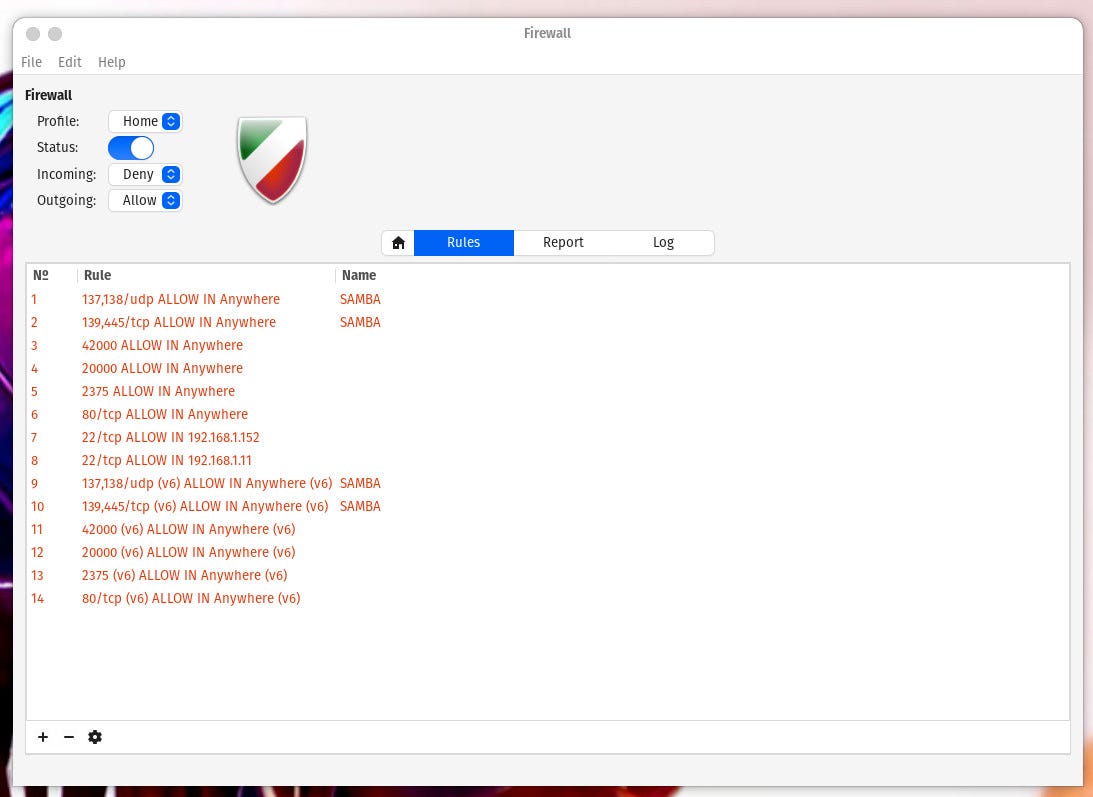
The GUFW device makes configuring your firewall even simpler.
Picture: Jack Wallen
As you may see, I have already got just a few UFW guidelines added. One factor to remember is that you just can not edit guidelines that have been added through the UFW command line. Let’s add the identical rule through the GUI that we simply did from the command line. Click on + after which (from the Preconfigured tab), choose the next:
- Coverage – Enable
- Course – In
- Class – All
- Subcategory – All
- Software – SSH
That alone will create the rule permitting all SSH visitors into your system. If, nonetheless, you wish to solely enable visitors from a single IP tackle, you will need to click on the Superior tab and fill out the next (Determine 2):
- Identify – any identify you need
- Coverage – Enable
- Course – In
- Interface – All Interfaces
- From – 192.168.1.152
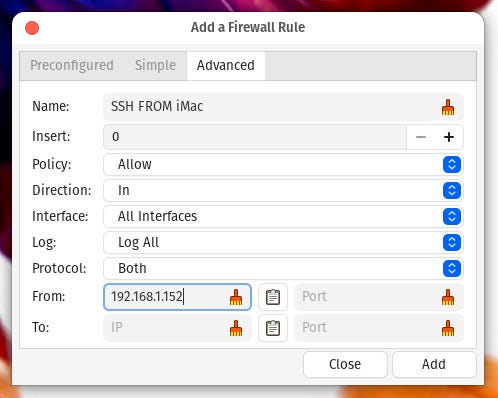
Including a rule to UFW to solely enable SSH visitors from IP tackle 192.168.1.62
Picture: Jack Wallen
Click on Add and your rule is inserted into the firewall.
And that, my mates, is your uncomplicated introduction to the Uncomplicated Firewall. However do not assume UFW is nothing greater than a really primary firewall system. You’ll be able to truly get significantly extra difficult however for the fundamentals, UFW is simple sufficient for anybody to make use of.
[ad_2]
Source link








