[ad_1]
Apache has released version 2.17.0 of the patch for Log4j after discovering points with their earlier launch, which came out on Tuesday.
Apache mentioned model 2.16 “doesn’t all the time shield from infinite recursion in lookup analysis” and defined that it’s susceptible to CVE-2021-45105, a denial of service vulnerability. They mentioned the severity is “excessive” and gave it a CVSS rating of seven.5.
“Apache Log4j2 variations 2.0-alpha1 by 2.16.0 didn’t shield from uncontrolled recursion from self-referential lookups. When the logging configuration makes use of a non-default Sample Structure with a Context Lookup (for instance, $${ctx:loginId}), attackers with management over Thread Context Map (MDC) enter information can craft malicious enter information that accommodates a recursive lookup, leading to a StackOverflowError that can terminate the method. That is also referred to as a DOS (Denial of Service) assault,” Apache defined.
They added that the newest challenge was found by Akamai Applied sciences’ Hideki Okamoto and an nameless vulnerability researcher.
Mitigations embrace making use of the two.17.0 patch and changing Context Lookups like ${ctx:loginId} or $${ctx:loginId} with Thread Context Map patterns (%X, %mdc, or %MDC) in PatternLayout within the logging configuration. Apache additionally urged eradicating references to Context Lookups within the the configuration like ${ctx:loginId} or $${ctx:loginId} the place they originate from sources exterior to the applying corresponding to HTTP headers or person enter.
They famous that solely the Log4j-core JAR file is impacted by CVE-2021-45105.
On Friday, safety researchers on-line started tweeting about potential issues with 2.16.0, with some identifying the denial of service vulnerability.
Dialogue about Log4j has dominated dialog all week. CISA released multiple advisories mandating federal civilian businesses within the US apply patches before Christmas whereas several major tech companies like IBM, Cisco and VMware have raced to handle Log4j vulnerabilities of their merchandise.
Safety firm Blumira claims to have discovered a new Log4j attack vector that may be exploited by the trail of a listening server on a machine or native community, probably placing an finish to the idea that the issue was restricted to uncovered susceptible servers.
Different cybersecurity corporations have discovered that major ransomware groups like Conti are exploring methods to reap the benefits of the vulnerability.
Google released a security report on Friday the place Open Supply Insights Crew members James Wetter and Nicky Ringland mentioned they discovered that 35,863 of the out there Java artifacts from Maven Central depend upon the affected Log4j code. Because of this greater than 8% of all packages on Maven Central have a minimum of one model that’s impacted by this vulnerability, the 2 defined.
“The common ecosystem impression of advisories affecting Maven Central is 2%, with the median lower than 0.1%,” Wetter and Ringland mentioned.
To this point, practically 5,000 artifacts have been patched, leaving greater than 30,000 extra. However the two famous that it will likely be tough to handle the problem due to how deep Log4j is embedded in some merchandise.
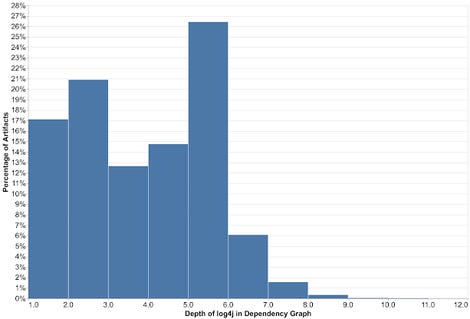
“Most artifacts that depend upon log4j achieve this not directly. The deeper the vulnerability is in a dependency chain, the extra steps are required for it to be mounted. For higher than 80% of the packages, the vulnerability is a couple of stage deep, with a majority affected 5 ranges down (and a few as many as 9 ranges down),” Wetter and Ringland wrote.
“These packages would require fixes all through all components of the tree, ranging from the deepest dependencies first.”
The 2 went on to say that after taking a look at all publicly disclosed crucial advisories affecting Maven packages, they discovered lower than half (48%) of the artifacts affected by a vulnerability have been mounted, that means it could take years for the Log4j challenge to be solved.
[ad_2]
Source link